Phishing Awareness Training: How to Design a Program That Changes Behavior
Completing a generic phishing awareness training program rarely equips an employee to detect or resist a real phishing attempt, especially when the program itself mainly checks a compliance box.
Even a well-intentioned employee can pass the annual quiz, earn the certificate, and still approve a fraudulent vendor change request after a vishing call from a cloned executive voice. Closing the gap between course completion and real-world competence is what separates a program that changes behavior from one that simply documents it, and it's why human behavior still plays a role in 60% of breaches.
This article shows how to build a phishing awareness training program that helps your workforce develop the reflexes needed to resist phishing attempts.
Key Takeaways
- Traditional training programs fail because they rely on an annual cadence, test only via email, deliver generic remediation, and run simulation and learning as separate tracks.
- Completing a phishing awareness training program rarely equips employees to resist real phishing attacks.
- Effective phishing awareness training programs must simulate real attacks, deliver contextual remediation, and measure risk continuously at the individual level rather than through population-level click rates.
- Turning phishing awareness from an annual compliance event to a continuous, behavior-changing practice requires a closed-loop model that turns live external threats into internal simulations, personalized lessons, and per-employee risk profiles.
What Is Phishing Awareness Training?
Phishing awareness training is the program a security team uses to teach employees to recognize and respond to social engineering attempts. It spans channels where business communication happens, including email, voice calls, SMS, and collaboration platforms like Microsoft Teams and Zoom. Security teams typically combine instructional content, simulated attacks, and post-failure remediation, running the program on a recurring cadence across a defined population of employees.
A phishing awareness training program succeeds when it changes how an employee acts in the moment an attacker confronts them: whether they slow down, verify, escalate, or refuse a request that looks legitimate on the surface.
Why Traditional Phishing Awareness Training Often Fails to Change Employee Behavior
Security teams often scope traditional phishing awareness training around compliance audits. That design choice results in an annual cadence, single-channel testing, generic remediation, and a learning experience disconnected from realistic simulation.
Annual Cadence Loses to Daily Attacker Velocity
Employees retain more when programs use spaced reinforcement, because memory decays rapidly after a single learning event. An employee who completes training in January and faces a targeted vishing campaign in April is operating on faded knowledge, and phishing training often delivers limited or short-lived improvement in simulated attack performance to begin with.
Annual cadence persists in part because regulators and auditors require evidence of training delivery and completion, but generally not evidence of behavior change. The institutional incentive favors the metric over the outcome.
Email-Only Tests Miss the Multi-Channel Reality
Enterprise attack campaigns now run through multi-stage attack chains that combine phishing emails, vishing calls impersonating IT support, SMS follow-ups, and messages inside collaboration platforms.
A program that only tests employees on email leaves every other channel untested, and employees default to the channel they've never practiced. The preparedness gap stays open until simulations cover the same channels and stages employees will face in real attacks.
Generic Remediation Doesn't Fix Specific Failures
Every phishing failure has a specific shape: the channel it happened on, the pretext that worked, and the action the employee took. A finance analyst who submitted data over a cloned voice call didn't make the same mistake as an engineer who clicked a follow-up SMS link, and routing both into the same 15-minute module on email phishing teaches neither the lesson they actually need.
Context-specific learning matters because knowledge an employee picks up in one context doesn't automatically transfer to action in another. The lesson has to match the failure on the channel where it happened, or it doesn't stick.
Simulation and Learning Are Treated as Separate Programs
Many programs run simulations and training as parallel tracks rather than one connected loop. Employees take a course in one quarter and get a phishing test in another, with no tight link between what they failed and what the program teaches them next.
Behavior change requires the two layers to operate as a closed loop: realistic simulation surfaces the specific failure, and contextual learning lands at the moment of that failure. A learning-only program produces informed employees who have never faced a test, while a simulation-only program produces click-rate dashboards without the remediation that turns failures into reflexes.
Three Principles That Make Phishing Awareness Programs Stick
Phishing awareness training programs that produce measurable behavior change share three design principles. They simulate real attacks across the channels attackers use, they tie each failure to contextual remediation in the moment, and they measure risk continuously at the individual level.
1. Simulate Threats That Mirror What Attackers Are Actually Sending
Simulations drawn from generic template libraries train employees to recognize the template itself. Simulations that use real lure copy, real landing page designs, and real pretexts pulled from active threat intelligence feel much closer to the attacks employees encounter in production, and they give employees repeated practice against the patterns that actually show up in their inbox or on their phone.
2. Land Remediation at the Moment of Failure
Immediate just-in-time feedback after a simulated phishing attack reduced susceptibility to the next one in a randomized controlled trial involving a large employee population. A brief, non-punitive, contextually relevant intervention at the point of the mistake outperformed the other remediation approaches researchers tested.
3. Measure Risk Continuously at the Individual Level
Population-level click rates obscure the individual risk distribution that programs need to address. In one dataset, 56% of employees failed at least one simulation, and a smaller subset accounted for repeated failures over time, indicating that disproportionate ongoing risk is concentrated in a small subset of employees. Per-employee risk profiles that track behavior across channels, over time, and across difficulty levels surface the patterns that flat click rates hide.
How to Design the Learning Layer of Phishing Awareness Training
The post-failure experience is where behavior change happens. Programs that contextualize the failure, personalize the lesson, and trigger training based on real, risky behavior outperform programs that route every employee into the same generic course.
Show the Employee Exactly What Just Happened
A branded fail page that replays the simulation, including the call transcript for voice or the exact email and landing page for phishing, contextualizes the experience for the employee. They see the specific lure, the specific channel, and the specific moment they made a decision. That context is the foundation on which the rest of the learning experience builds.
Tailor the Lesson to How They Failed
Two employees can fail the same simulation in different ways. One submits credentials over the phone; the other clicks a follow-up link in an email the voice agent sent mid-call. The skill gap differs in each case, and personalized quizzes tied to function, scenario, and specific failure mode reinforce the right lesson for each individual. The engineer who submitted data over the phone gets a quiz on phone-based data disclosure; the one who clicked the link gets a quiz on link verification.
Trigger Just-in-Time Training From Real Risky Behavior
Real employee actions provide a strong signal for training. When identity and access management tools detect that an employee clicked a flagged URL in production or attempted a risky login, automatically assigning a brief, relevant lesson at that moment converts a live risk event into a learning event. The training arrives at the moment of the behavior rather than on the next quarterly cycle.
How to Design the Simulation Layer of Phishing Awareness Training
A simulation layer that drives behavior change should cover the main channels where business communication occurs, run as a single global program rather than a dozen translated ones, and draw scenarios from threats that actively target the organization.
Cover Every Channel Where Business Communication Happens
For an enterprise program, the channel set should extend beyond email to include vishing, help desk impersonation, SMS, and collaboration platforms such as Microsoft Teams and Slack. Voice deserves particular attention as attackers are now combining email-bombing and vishing attacks during initial access. Any channel the program excludes from simulation leaves employees untested there.
Run One Global Campaign That Localizes Per Employee
Running separate campaigns for each country consumes bandwidth that most security teams don't have. A single global campaign that uses scenario localization through identity provider integration produces more consistent coverage and avoids the operational overhead of managing dozens of parallel programs.
Pull Simulation Content From Live Detected Threats
Static template libraries can teach employees to recognize the simulation format. Simulations that draw from live threats targeting the organization keep content relevant and keep rotation moving. If a brand-impersonation campaign runs against the organization today, the same lure can run as an internal simulation tomorrow, while the employee's reaction is still calibrated to what attackers are sending right now.
How to Measure Behavior Change Across the Program
A stronger measurement layer integrates multiple data points, builds a per-employee risk profile, compares behavior across multiple channels, and benchmarks performance against industry peers and internal departments to surface the patterns that drive program decisions.
Build a Risk Profile for Every Employee
Each employee should have a unique profile that includes a personal risk score with an explanation of its drivers, a consecutive fail streak count, response speed, data submission rate, quiz pass rate, and a per-channel breakdown. An LLM-generated behavioral summary that synthesizes patterns across simulations and training, with recommendations on what to test next, turns raw data into actionable guidance for program operators.
Compare Behavior Across Every Channel You Defend
Organizations need a measurement model that captures resilience across every channel they defend. When organizations run multi-channel simulations for the first time, non-email failure rates often run high because employees have never practiced them. Tracking click rates, data submission rates, and reporting rates across email, voice, SMS, Teams, and Zoom can produce a multi-channel risk baseline for organizations.
Benchmark Against Industry Peers and Internal Departments
Internal benchmarking reveals which departments are responding well and which require targeted intervention, while industry benchmarking helps contextualize the organization's risk posture relative to its peer set. Department-level risk comparison and repeat-offender tracking over time surface the specific concentrations of risk that justify program investment for leadership.
How Doppel Closes the Loop Between Phishing Threats and Training
Designing a phishing awareness training program that changes behavior requires a closed loop between the threats attackers are running externally and the simulations and lessons employees see internally. Most tools cover one side of that loop or the other, which is why the loop rarely closes in practice.
Doppel is the AI-native Social Engineering Defense (SED) platform that closes that loop in one place. It unifies Digital Risk Protection (DRP) and Human Risk Management (HRM) into a single system.
It detects and dismantles impersonation and phishing infrastructure attacking the organization from the outside, then feeds those same live tactics into the simulations and coaching employees see on the inside.
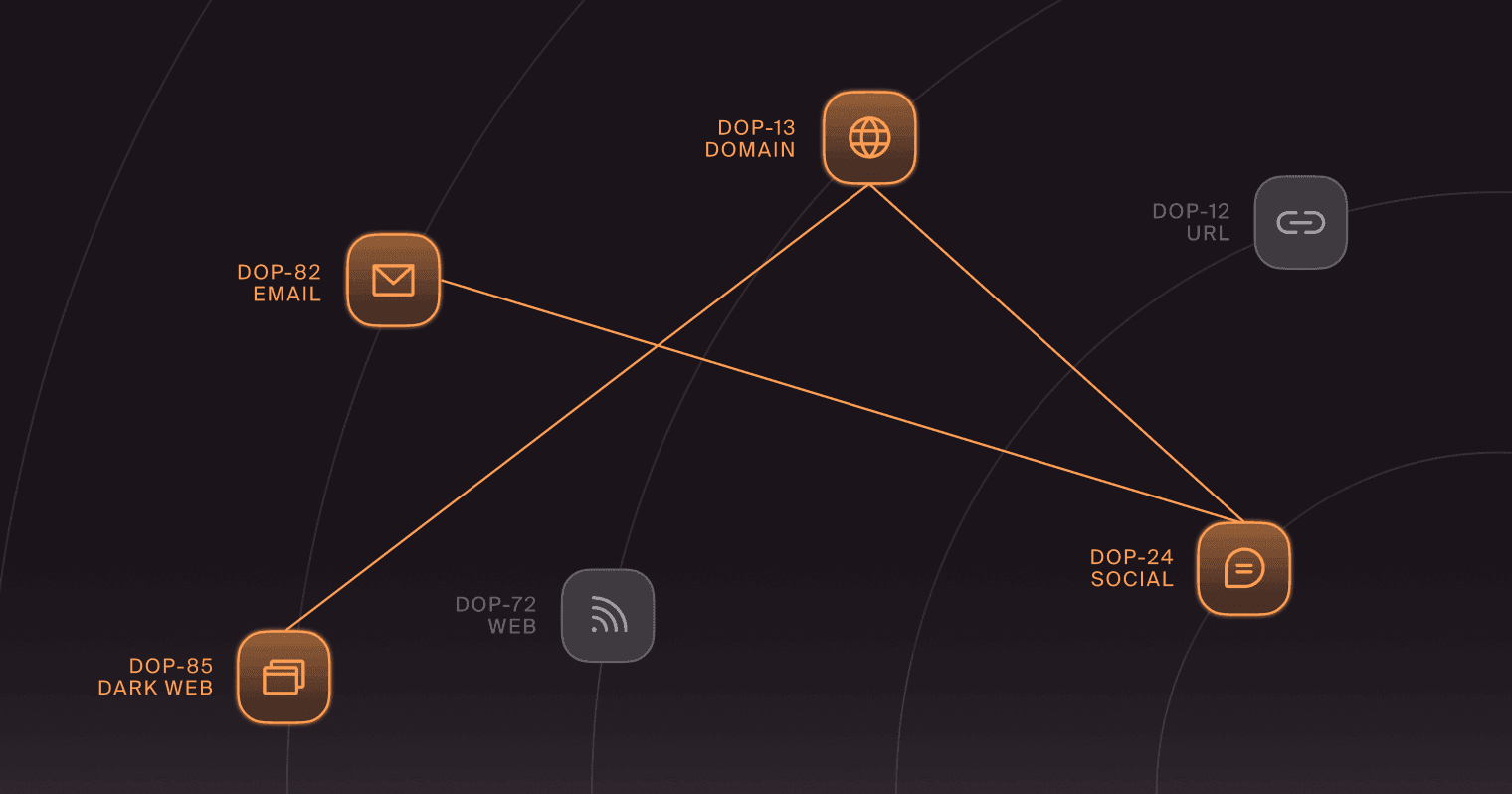
The detection side correlates domains, profiles, phone numbers, ads, and messaging signals in the Doppel Threat Graph, then takes down attacker infrastructure across channels before the same patterns reach more employees.
When Doppel detects an external threat through its Brand Protection and Executive Protection products, security teams can convert it into employee training with one click via Doppel Simulation. From there, the platform clones the lure copy, landing page, and infrastructure pattern of a real phishing campaign, defangs them, and wires them into a simulation tied to a live attack.
The post-failure experience remains tied to the specific way each employee failed, with personalized quizzes, contextual coaching, and role-based training based on actual behavior triggers. Simulation carries that model across email, voice, SMS, Microsoft Teams, Zoom, and Telegram, with voice agents that hold live, dynamic conversations and can pivot mid-call to send follow-up emails or texts.
Move Phishing Awareness From Annual Event to Continuous Practice
Behavior change is the only outcome that matters in phishing awareness training, and it's the one that fragmented programs consistently miss.
When external detection, internal simulation, and post-failure coaching each run on their own track, every layer ends up optimizing for its own metric: completion rates for training, click rates for simulations, takedown counts for threat intel. None of those numbers tells a security leader whether an employee will actually hesitate the next time a cloned voice asks them to wire money or a Teams message follows up on a vishing call.
What ties those layers together is a shared signal. The attacker's tactics that hit the organization on Monday should shape the simulation that an at-risk employee runs on Tuesday and the coaching they receive on Wednesday. Without that signal moving across layers, employees end up rehearsing on yesterday's templates while attackers iterate on tomorrow's lures, and the handful of users responsible for most repeat failures stay invisible inside aggregate dashboards.
Doppel is built to make that signal move. External impersonation and phishing infrastructure feed directly into Dynamic Simulation; post-failure coaching matches the channel and pretext that tripped each employee; and individual risk profiles surface the users who need attention before attackers find them.
Preview Doppel Simulation or request a personalized demo to see a live walkthrough of how an external takedown becomes an internal simulation, and how the loop holds up against the threats targeting your organization today.