A New Standard for Unified Defense in Depth
For years, social engineering has been the most common and effective attack vector in cybersecurity. What’s changing now is the speed and precision at which it’s being executed. With the rise of generative AI, these attacks are becoming more adaptive, more scalable, and vastly harder to detect, giving adversaries an asymmetric advantage that targets human trust as much as technology.
Modern social engineering is no longer a series of isolated incidents. It’s a coordinated, AI-driven lifecycle designed to exploit the cracks between fragmented security tools and disconnected defenses.
Building real resilience starts with understanding how these campaigns actually work in the wild. They’re a synchronized sequence, beginning with external setup and infrastructure, then moving deeper into targeted social and conversational manipulation. You can’t stop what you only see in pieces; you have to see the entire chain.
When your defenses are as integrated and intelligent as the attacks themselves, you don’t just observe the chain, you break it.
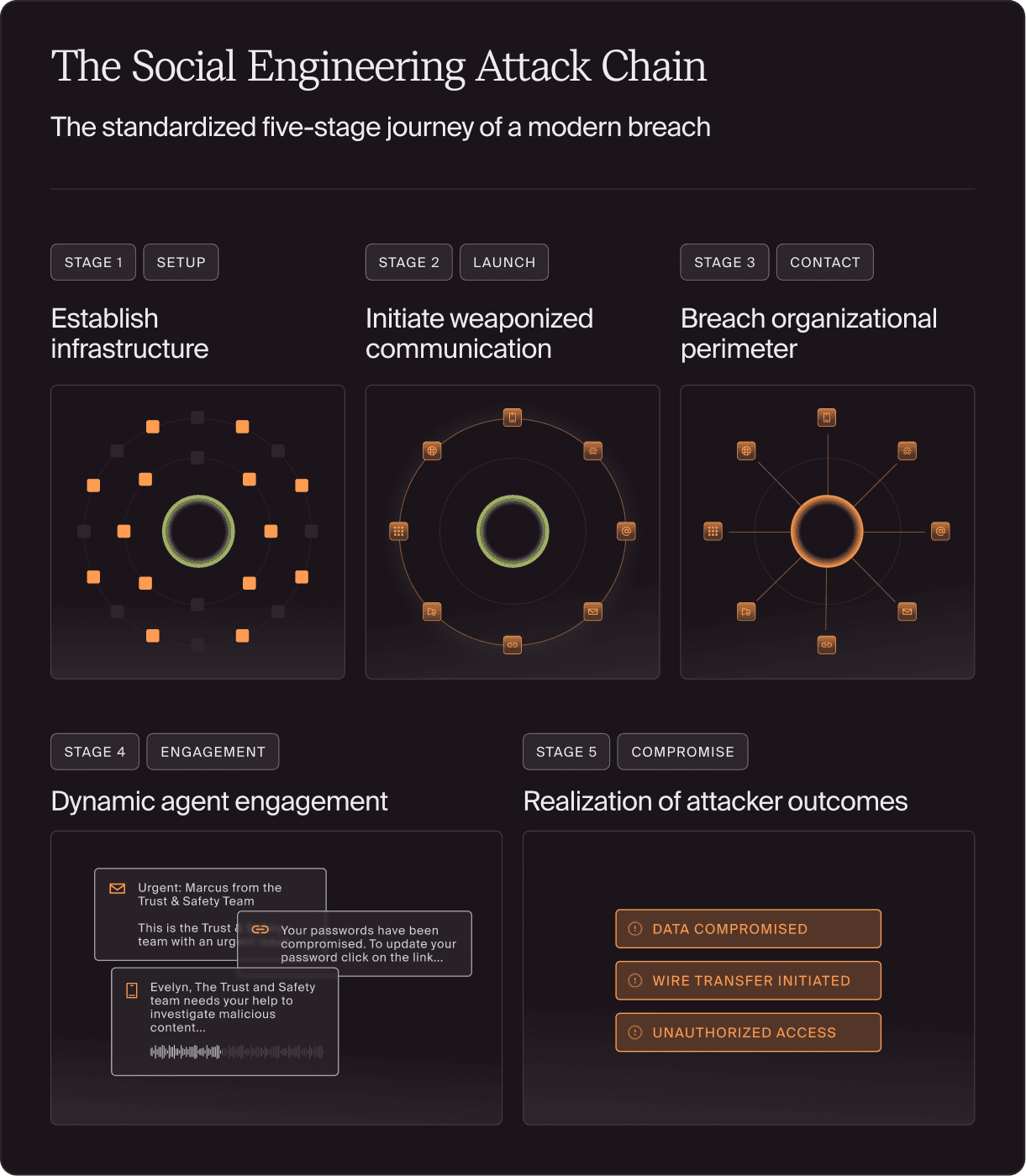
The Social Engineering Attack Chain
We recognize this as The Social Engineering Attack Chain. The standardized five-stage journey of a modern breach:
| Stage 1 | Setup: Establish infrastructure Attackers use an arsenal of weapons including Agentic AI to rapidly build high-fidelity infrastructure. By mimicking your brand, leadership, or employees, they establish a baseline of trust. What this looks like: Look-alike domains, root assets, deepfake personas, and deceptive social profiles. |
| Stage 2 | Launch: Initiate weaponized communication Once the attack infrastructure is built, the attacker uses it to weaponize communication across multiple channels. Whether the weapon is a traditional malicious file or a psychological lure, this stage is the delivery. What this looks like: Phishing emails, Smishing (SMS), Vishing (Voice), or malicious Social Ads. |
| Stage 3 | Contact: Breach organizational perimeter The threat achieves presence in the target’s digital environment. It is the transition from an external delivery to a live, actionable lure residing on the user's device. What this looks like: A malicious message appearing in a primary inbox, an urgent SMS notification, or a connection request in a professional app. |
| Stage 4 | Engagement: Dynamic agent engagement Execution of the “Interactive Payload”—the transition from a static lure to a live, multi-channel exchange. The attacker (human or AI) uses adaptive dialogue to direct the victim’s interaction with malicious infrastructure. This is the critical window where the attacker facilitates target engagement with deceptive environments such as spoofed domains or MFA intercepts, to convert an initial contact into a verified compromise. What this looks like: Triggering interactive payloads, directing victim interaction with deceptive domains, sustaining adaptive dialogue, or deploying synthetic voice to facilitate technical workflows. |
| Stage 5 | Compromise: Realization of attacker outcomes The final phase where the attacker fulfills their intended motive and the organization incurs a tangible loss. This stage represents the conclusion of the engagement window, where the preceding interaction successfully results in a breach of trust or assets. What this looks like: Unauthorized acquisition of real-time corporate data, fraudulent wire transfers, stolen credentials, or system-wide ransomware deployment. |
The Evolution of the Payload: From Contact to Compromise
The Lockheed Martin Cyber Kill Chain® and MITRE ATT&CK® provide an essential foundation for technical defense. These frameworks excel at tracking infection-based attacks, mapping how a malicious file (the technical payload) is weaponized, delivered, and executed.
However, the threat landscape has expanded from technical vulnerabilities to human ones. Today’s social engineering is interaction-based, meaning the "payload" is no longer a static file, but the conversation itself. While legacy frameworks prioritize technical reconnaissance, Generative AI now automates the labor of target research and content creation. This effectively compresses the attack timeline to machine speed, making the velocity of compromise, rather than just the method—the primary risk.
In an era of AI-native deception and Business Email Compromise (BEC), attackers frequently bypass the 'Exploitation' or 'Installation' phases entirely. There is no malicious code to trigger a signature-based alert because the attacker exploits human psychology through legitimate channels. By tracking the Engagement phase, the Social Engineering Attack Chain provides the visibility needed to stop these "payload-evolved" threats before they reach the stage of Compromise.
Continuous Attack Lifecycle vs. Fragmented Defense
While the Attack Chain is a continuous journey for the attacker, it remains fragmented for the defender. Most organizations manage the "outside" and "inside" of the chain as separate technical problems.
Millions are invested in monitoring the outside: Stage 1 (Setup) and Stage 2 (Launch), using Threat Intelligence (who’s attacking and how) and External Attack Surface Management (discovery of what you have exposed). Yet these tools exist in a separate universe from the inside: Stage 4 (Engagement) covered by Human Risk Management (HRM) and active in-line defenses.
The critical failure is that signals die at the perimeter, creating a blind spot at Stage 3 (Contact). Because external data never reaches internal defenses, employees are left to face sophisticated, AI-informed interactions with generic, uninformed training. In the age of machine-speed deception, a fragmented defense is no defense at all.
Doppel’s Unified Defense in Depth
For decades, the security industry has relied on the "human firewall" as the final filter for social engineering. In the age of AI-native deception, expecting employees to detect every synthetic threat creates an unsustainable operational risk. Doppel is designed to shift this burden. The individual shouldn't be the primary intercept for technical deception. The platform must be the technical fail-safe.
Doppel has moved beyond fragmented point solutions to establish a unified architecture aligned with the end-to-end social engineering lifecycle. By standardizing the Social Engineering Attack Chain, we synchronize defense layers through a single, intelligence-driven engine: The Doppel Threat Graph.
The Threat Graph serves as our central nervous system, continuously linking disparate signals: look-alike domains, social handles, and phone numbers, into a unified, campaign-level view. This real-time correlation allows us to expose an attacker's entire infrastructure at once, ensuring that intelligence gathered on the "outside" is immediately used to automate and inform defenses on the "inside".
This closed-loop intelligence is operationalized through three synchronized defense layers, starting with the proactive elimination of the threat at its source:
- Proactive Infrastructure Disruption
We don't just monitor for risk; we break the chain at the Staging phase. Our platform (Digital Risk Protection) identifies and dismantles malicious infrastructure in the wild—fake domains, deepfake personas, and deceptive social accounts—before the first message is ever launched. - Threat-Informed Resilience
We harden the human element by moving beyond generic "checkbox" training. We deliver hyper-realistic simulations derived directly from the live attacker tactics our platform (Human Risk Management) is currently intercepting, ensuring your employees are prepared for the exact threats they will face. - Active Inline Defense
Doppel is architected to sit directly within the live communication stream. Our roadmap introduces active inline detection to monitor the flow of communication during the ‘Dynamic Agent Engagement’ phase. By analyzing reasoning-based dialogue in real-time, this capability identifies the "Interactive Payload" as it unfolds, surfacing deceptive intent within a conversation before it can result in a compromise.

The CISO’s Next Move
The modern CISO must move the organization from a posture of managing tools to a posture of managing the lifecycle. The "Bottom Line" is no longer about adding more layers; it is about eliminating the gaps between them.
A unified platform is the only way to outpace the velocity of AI-native deception. By linking external visibility to internal in-line enforcement, you ensure that your defense adapts as quickly as the attacker. The era of the human as the last line of defense is over. The era of the platform as the final fail-safe has begun.
This is the new mandate for social engineering resilience.
