Doppel Named Official Partner of the New York Knicks
Partnership to Showcase Doppel to Knicks Widespread Audience Through In-Arena, Digital and Out-Of-Home Assets
Financial Services & Fintech brands remain one of the most consistently targeted sectors for impersonation and fraud, but Doppel telemetry from late 2025 through early 2026 highlights a meaningful shift, not just in volume, but in how attacks are executed.
Financial Services & Fintech
Report Date: 04/22/2026
Financial Services & Fintech brands remain one of the most consistently targeted sectors for impersonation and fraud, but Doppel telemetry from late 2025 through early 2026 highlights a meaningful shift, not just in volume, but in how attacks are executed. What were once fragmented phishing attempts have evolved into coordinated, multi-channel social engineering campaigns designed for scale, persistence, and higher conversion rates.
From December through January, activity settled into a holiday baseline, reflecting a more distributed threat landscape across industries. That baseline did not hold for long. Beginning in February, and accelerating sharply into March, attacker activity surged. By March, indexed activity had increased nearly fourfold compared to January, signaling a rapid escalation in both campaign volume and operational sophistication.
This increase is not simply a matter of more activity. It reflects more effective attack strategies. Adversaries are leveraging platforms like social media, paid advertising, messaging applications, and email in tandem, creating layered engagement funnels that guide victims from initial exposure to final compromise. The result is a threat environment where campaigns can scale quickly, adapt in real time, and sustain pressure over extended periods.
Early April data indicates that this momentum is continuing rather than peaking. Even as a partial month, activity is tracking above March levels, reinforcing that this is not a short-lived spike tied solely to seasonal factors. While tax season remains a key driver for financial targeting, the data points to a broader evolution in attacker behavior, one that prioritizes reach, automation, and cross-channel coordination.
Taken together, these trends underscore a critical reality: the threat landscape for Financial Services is not only growing, but becoming more structured and efficient. Understanding this shift is essential for anticipating where attackers will move next and how to effectively disrupt them.
Total activity by month (indexed)
While overall activity surged, domain-based infrastructure followed a more measured trajectory, rising steadily but not at the same pace as total activity.
This divergence is important. Domains are no longer the primary driver of attack volume. They are increasingly the final step.
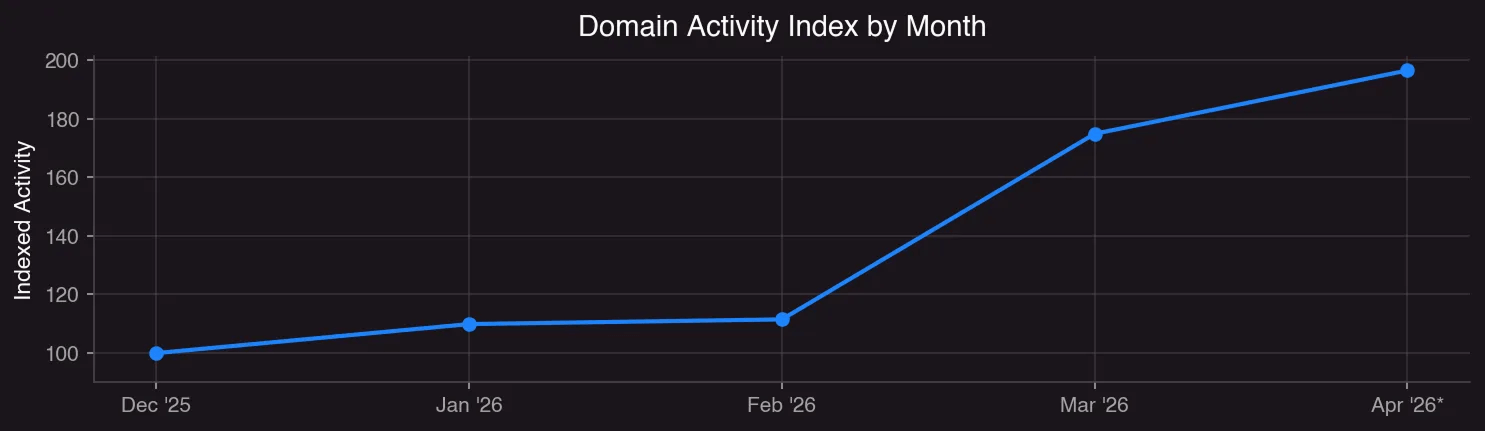
Domain activity by month (indexed)
The real expansion is happening earlier in the attack chain, where adversaries are focusing on scalable distribution and engagement channels. Domains still play a critical role, but more often as conversion infrastructure rather than discovery.
Where the activity originates provides a clearer picture of how attacker behavior is evolving over time.
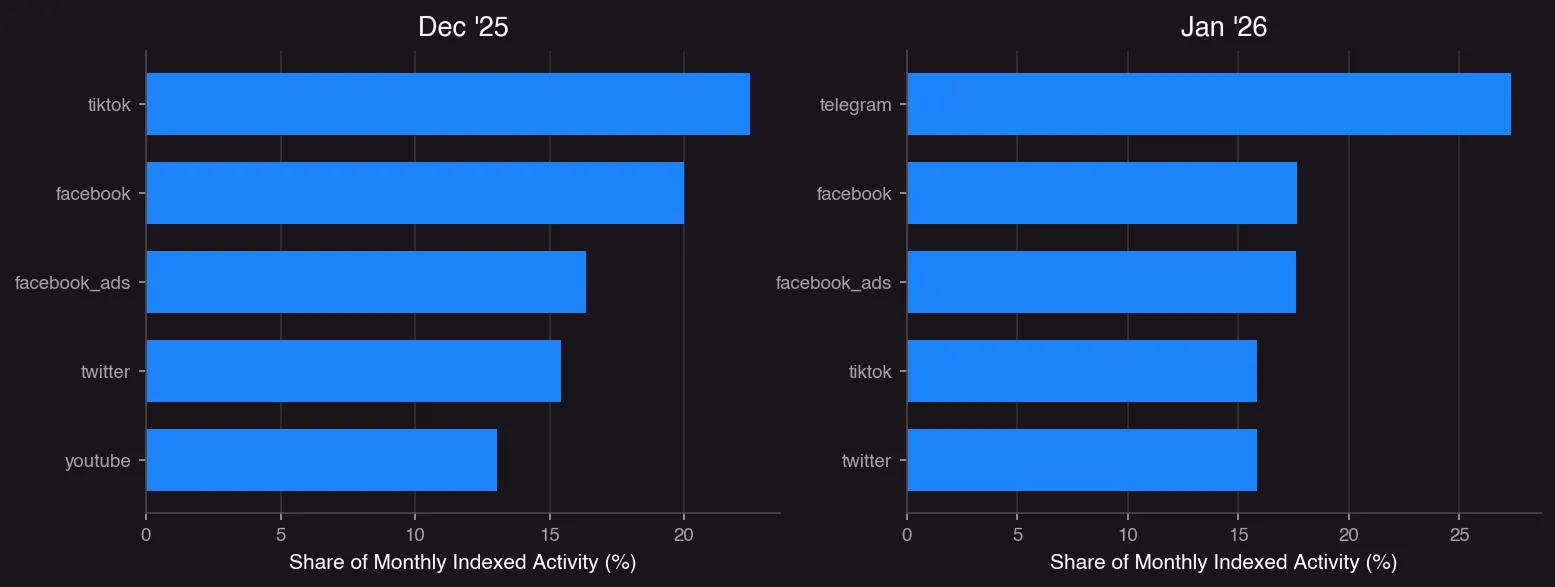
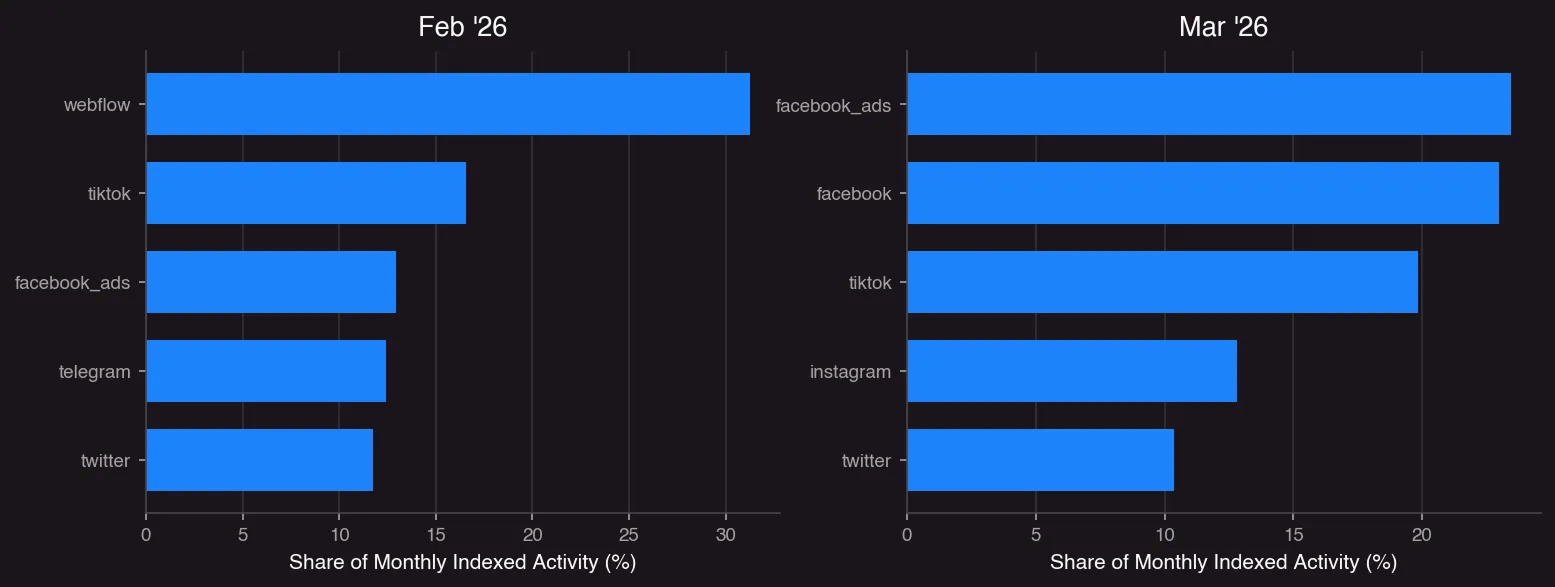
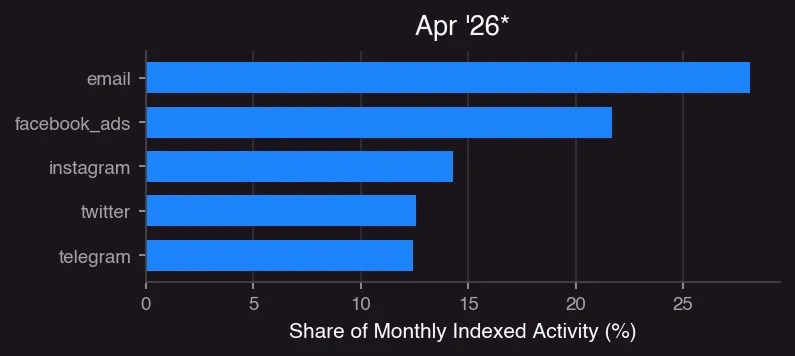
Top Sources of Activity
In December, activity was distributed across hosted platforms, social networks, and messaging channels. By January, messaging platforms such as Telegram became more prominent, alongside rapidly deployable hosting infrastructure. February showed increased use of higher-fidelity hosting platforms such as Webflow, indicating a move toward more convincing impersonation experiences.
By March, the pattern becomes clear. Facebook Ads and Facebook emerge as dominant sources of activity, alongside TikTok and Instagram. This represents a meaningful shift from earlier months, where activity was more distributed across platform types.
This concentration suggests that attackers are increasingly prioritizing paid distribution as a core component of their campaigns, using advertising platforms to place malicious content directly in front of users rather than relying solely on organic discovery. For financial brands, this approach is particularly effective. Ads can closely mimic legitimate services, appear in trusted environments, and create urgency aligned with real financial workflows.
April expands on this model. Email emerges as a leading source alongside continued activity across social and messaging platforms. This reflects a broader shift toward multi-channel campaign design, where attackers combine paid, organic, and direct communication channels to maximize reach and conversion.
At the same time, it is important to interpret these shifts with context. The increase in activity across platforms such as Facebook Ads reflects both a real change in attacker behavior and improved detection coverage. Enhanced visibility into these surfaces contributes to the magnitude of observed spikes, but the underlying trend toward scaled, distribution-first campaigns is clear.
What this ultimately signals is a change in attacker strategy. Campaigns are no longer centered solely on building convincing phishing infrastructure. They are focused on scaling access to victims, and distribution channels are now the primary lever.
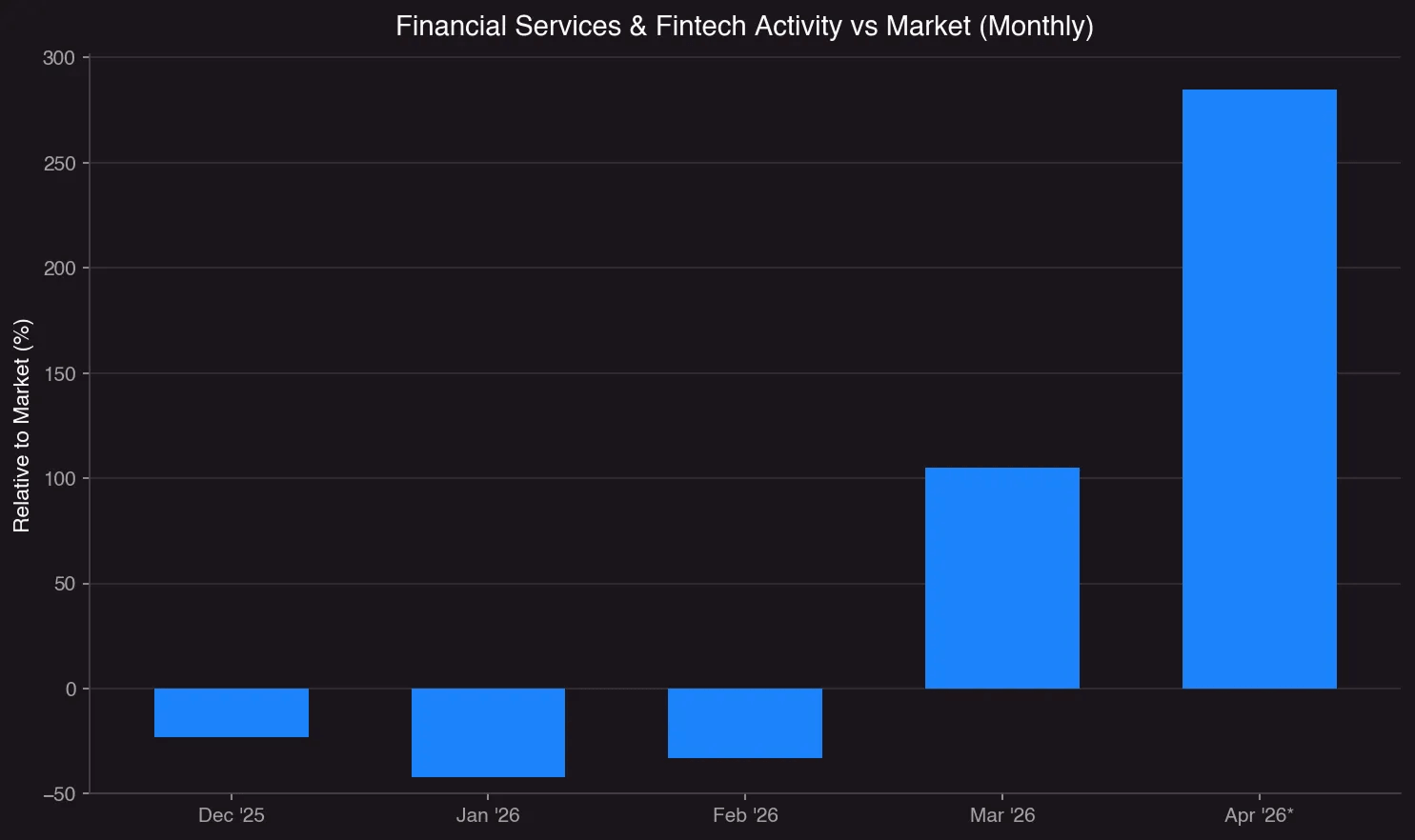
Comparing Financial Services & Fintech activity to the broader market highlights how sharply attacker focus has shifted.
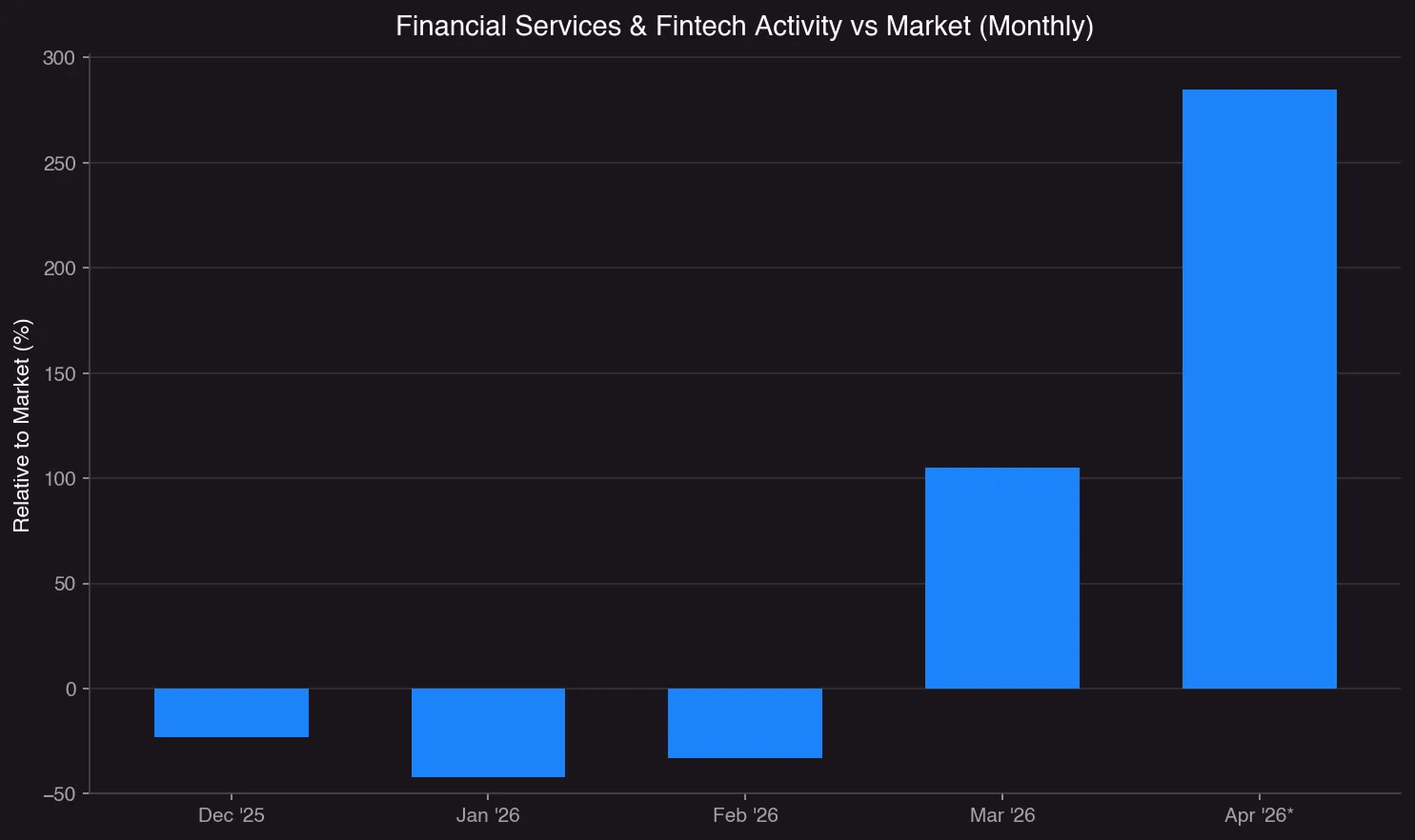
April is projected based on partial month data.
Financial Services & Fintech activity trailed the broader market through much of the winter period. In December, indexed activity was already below market levels, and this gap widened further in January, where the vertical lagged the broader ecosystem significantly. February showed some recovery, but activity remained below the market baseline, indicating that attacker focus during this period was more distributed across industries.
This pattern shifted decisively in March. Financial Services experienced a rapid increase in indexed activity, rising to more than double the broader market on a relative basis. The transition is abrupt rather than gradual, with a clear inflection beginning mid-month and accelerating through the end of March. This type of movement is consistent with concentrated campaign activity rather than organic growth.
That elevated pressure extends into April. Even as a partial month, activity is tracking significantly above March levels. Indexed activity suggests Financial Services is now operating at nearly three times the broader market baseline.
This aligns with historical patterns where tax season drives increased targeting of financial institutions and their customers. However, the scale and persistence of the increase also reflect a broader evolution in attacker behavior. Expanded use of multi-channel engagement, growing reliance on paid distribution, and emerging vectors such as voice-based social engineering all contribute to a more aggressive and adaptive threat environment.
Importantly, tax season acts as a catalyst, not a boundary. The sharp increase observed in March and April demonstrates how quickly attacker focus can shift and scale. As tactics evolve and regulatory expectations expand, maintaining continuous visibility and protection across channels remains critical.
Across the dataset, a consistent attack flow emerges. Campaigns begin with discovery through ads, social posts, or email, move into engagement through messaging or interaction, and ultimately drive victims to hosted pages or spoofed domains where compromise occurs.
This multi-step structure allows attackers to maximize both scale and effectiveness. Distribution channels generate reach, engagement channels build trust, and infrastructure handles conversion.
At the same time, the infrastructure supporting these campaigns has become more flexible. Platforms such as Webflow and other hosted services enable rapid deployment of phishing pages that closely resemble legitimate financial services.
When individual components are taken down, they can be quickly replaced. This allows attackers to maintain momentum with minimal cost or disruption. As a result, focusing on isolated takedowns is often insufficient. Effective disruption requires visibility into the full campaign, including domains, hosting providers, social accounts, and advertising activity.
Without that broader view, defenders risk removing a single entry point while the larger campaign continues operating through parallel or regenerated components.
The sharp increase observed from February to March, likely amplified by tax season, highlights how quickly attackers can scale when conditions are favorable.
Financial institutions should expect continued use of social engineering tactics that combine paid distribution, trusted platforms, and convincing impersonation to drive fraud outcomes. The data shows that attackers are not just increasing activity, but refining how they reach and influence victims.
The threat landscape for Financial Services & Fintech is now defined by scalable, multi-channel campaigns. Domains remain important, but the most impactful activity is occurring earlier in the attack chain, across social platforms, advertising ecosystems, and direct communication channels where attackers can reach victims at scale.
This is not a temporary shift. It reflects a more mature and efficient attack model that will continue to evolve. Organizations that adapt their defenses to this reality will be better positioned to reduce risk, while those that focus only on traditional indicators may struggle to keep pace.
Doppel identifies and disrupts social engineering threats across multiple channels commonly leveraged by threat actors, including domains, social media, email, and telecom. By correlating activity across these channels, Doppel provides a more comprehensive view of campaigns rather than isolated incidents, and autonomously dismantles attack infrastructure. Insights from these threats inform targeted training and simulation programs, helping organizations better prepare employees for real-world attack tactics. This approach enables organizations to understand how social engineering attacks develop, spread, and ultimately impact their brand, employees, and customers.
Channels in Scope:
| Category | Description |
|---|---|
| Domains | Streams domain registrations and SSL certificates, analyzes website content, conducts phishing-kit analysis, and computer vision (OCR) to detect and categorize domain threats with better detections, complete coverage and faster takedown times. Confirmed threats are automatically taken down. Includes 24/7 service delivery support through Slack, Discord, Telegram, and Teams. |
| Uses tools like honeypots and phishing inbox automation (which connects to endpoint solutions like Proofpoint) to prevent phishing of employees and protect clients’ brand reputations. | |
| Applications | Maintain consumer trust and protects revenue by using native integrations to scan the Apple app store, Google Play, APK sites, and other app marketplaces to detect fake mobile apps, and browser extensions and automatically take them down. |
| Social Media | Leverage AI to scan social media platforms in real time using native integrations, content analysis, and OCR analysis to detect and takedown fake accounts and malicious posts. Faster takedowns are empowered through strategic relationships and APIs that enable automatic removal of harmful content. |
| Vishing/Smishing/Telecom | When a company receives a report about a scam phone call or text through their support, they can forward it to Doppel Vision. Reports the scam to the telco to get it taken down, protecting the client’s brand reputation. |
| Ecommerce | Automatically detects and takesdown counterfeit listings across e-commerce marketplaces. |
| Darkweb | Monitors darkweb for PII leakage, data leakage, and credential dumps associated with Brands and their executives. |
| Crypto / NFT | Automatically detects and removes scam tokens and NFTs impersonating Fidelity across centralized Report these tokens to block explorers. Wallet-enabled websites and other crypto-related malicious sites are automatically reported to wallet providers including MetaMask, Phantom, Coinbase Wallet and other wallets to block these sites within minutes upon reporting. |
Doppel protects individuals and brands from AI-powered impersonation, phishing, fraud, and social engineering by dismantling attacker infrastructure and building resilience through training and simulation.
Doppel's comprehensive Digital Risk Protection solution detects threats across multiple channels, links alerts into a real-time threat graph, and offers AI-driven infrastructure disruption. These threats inform phishing simulation campaigns and security awareness training to offer robust Human Risk Management capabilities that strengthen employee defenses through next-generation training and testing.
Doppel's mission is to protect the world from social engineering attacks every day. Founded in 2022, Doppel is an AI-native platform designed for social engineering defense.
Median Takedown Time Domains, Social Media, Paid Ads
<10h
Faster takedowns on emerging threat vectors than our competitors.
Indicators Analyzed Daily
+1B
Faster takedowns on emerging threat vectors than our competitors.
Trusted Customers
200+
Companies have chosen Doppel