You’re a CFO, and 4:45 on a Friday comes around. Your phone buzzes with an urgent text message.
It’s the CEO.
“I’m boarding a flight. We need to close the acquisition of that competitor by 5:00PM. I just emailed you the vendor details. Wire $2.5 million immediately.”
Your heart races. The pressure is immense. You want to execute the request seamlessly and be a reliable partner to the business.
But you pause.
This is the type of social engineering that threat actors often use. They know the fastest way to steal money from a company is to bypass the firewall and manipulate the people who control the bank accounts.
You need a standardized, emotionless response plan.
Here’s the 15-minute response plan every CFO and finance leader should execute when faced with an urgent executive wire request.
Minute 1 to 3: Hard Pause & Isolate
The attacker’s entire strategy relies on artificial urgency. They want to trigger your fight-or-flight response so you bypass logical security awareness training (SAT).
Your first action is to do absolutely nothing.
- Stop the Interaction: Don’t reply to the email. Don’t text back the number that just messaged you. Don’t answer an incoming call from that specific number.
- Isolate the Request: Take a breath and objectively look at the communication.
- Assume Compromise: Treat the request as hostile until definitively proven otherwise. Remember that executive accounts are prime targets for takeover.
Attackers manufacture stress to force mistakes, so by taking just three minutes to simply pause and assess, you immediately neutralize their primary weapon.
Minute 4 to 7: Out-of-Band Verification
You can’t verify a request using the same channel it was received on. If the attacker compromised the CEO’s email or is impersonating them, replying to that email only connects you with the attacker.
Establish an out-of-band communication channel. This means switching to a secondary, trusted method of contact that the attaker can’t intercept.
- Call the Known Number: Pick up the phone and dial the CEO’s known phone number. Don’t use any phone number provided in the suspicious email or text message.
- Demand Voice Verification: If the CEO answers, ask them to verbally confirm the wire transfer details.
- Use a Video Sync: If the request is substantial, mandate a Zoom meeting or Microsoft Teams video call.
- Leverage a Shared Secret: Some organizations establish a duress word or shared secret among the C-suite for this scenario. Ask the executive to provide the predetermined phrase.
If you can’t reach the CEO through an established, trusted channel, the wire transfer can’t happen. There are no exceptions to this rule.
Minute 8 to 10: Cross-Check Financial Controls
While you’re attempting to verify the request out of band, engage your internal financial safeguards.
No single executive, not even the CEO, should have unilateral authority to bypass established financial controls.
- Review Vendor Details: Cross-reference the requested routing and account numbers against your vendor database. Are they a new vendor? Has an existing vendor suddenly changed their payment details?
- Engage Dual Approval: Immediately notify your controller or a secondary finance executive. State clearly that an unusual request has been made and that dual-approval protocol is locked in place.
- Consult General Counsel: If the request involves a ‘secret’ acquisition or strict NDA, pull in the company’s legal counsel. The legal team will know if an acquisition is actually in progress.
If the request is legitimate, the CEO will respect the adherence to financial governance. If they get angry, it’s highly likely that you’re dealing with a threat actor.
Minute 11 to 15: Escalate & Report
By minute eleven, you have either verified the request is legitimate, or you’ve confirmed it’s a social engineering attack.
If it’s an attack, move quickly to secure the organization. The attacker has shown their hand, and they may be embedded in your network.
- Alert the Security Team: Immediately notify the CISO or your IT security operations center. Provide them with screenshots of the text messages and forward the suspicious emails as attachments.
- Lock Down Compromised Channels: If the email came from the CEO's actual internal account, IT must immediately force a password reset and revoke all active session tokens for that account.
- Issue an Executive Alert: Threat actors often target multiple executives simultaneously. If the CFO did not fall for the scam, the attacker might try the VP of Finance next. Warn the leadership team that an active impersonation campaign is underway.
Spotting the Red Flags: Real Executive Request vs Social Engineering Attack
Threat actors are incredibly sophisticated, but they leave behavioral clues.
When evaluating a request during those first few critical minutes, look for the subtle differences between a standard corporate transaction and a social engineering attempt.
Scenario | Real Executive Request | Social Engineering Attack |
Tone | Professional, standard business communication | Highly emotive, aggressive, or unusually familiar |
Urgency | Respects standard banking hours and processing times | Demands immediate action, possibly late on a Friday or over a weekend |
Secrecy | Follows established procurement and reporting structures | Demands absolute secrecy and explicitly forbids speaking to others |
Payment Method | Uses established corporate vendor accounts and standard routing | Requests a sudden change in routing numbers, international wires, or cryptocurrency |
Channel | Initiated through official corporate email or a scheduled meeting | Initiated via a personal email address, SMS text, or an unscheduled phone call |
AI is Evolving Executive Impersonation
The 15-minute response plan outlined above is critical, but it’s becoming harder to execute.
In the past, spotting a fake CEO email was relatively easy. The spelling was often atrocious, and the grammar was stilted.
Today, attackers use large language models (LLMs) to write flawless emails that perfectly mimic your CEO's exact communication style. They scrape LinkedIn and corporate blogs to understand the specific terminology your company uses.
Even more terrifying is the rise of deepfake AI voice and video scams.
A threat actor can scrape thirty seconds of your CEO speaking on a podcast or an earnings call. They can then clone that voice perfectly.
When you attempt your out-of-band verification and call the CEO, the attacker might intercept the call and impersonate your CEO, using their exact voice, including their regional accent and pacing.
This means your security posture can no longer rely on spotting a typo. It must rely on unbreakable behavioral workflows.
Social Engineering Defense (SED): Training Leadership for the Inevitable
You can’t wait until 4:45 PM on a Friday to figure out if your CFO knows how to handle a targeted attack.
Your executive team is your most heavily targeted attack surface. They control the funds, the data, and the access. They require specialized, executive-tier protection.
This is why human risk management (HRM) is pivotal for a security program.
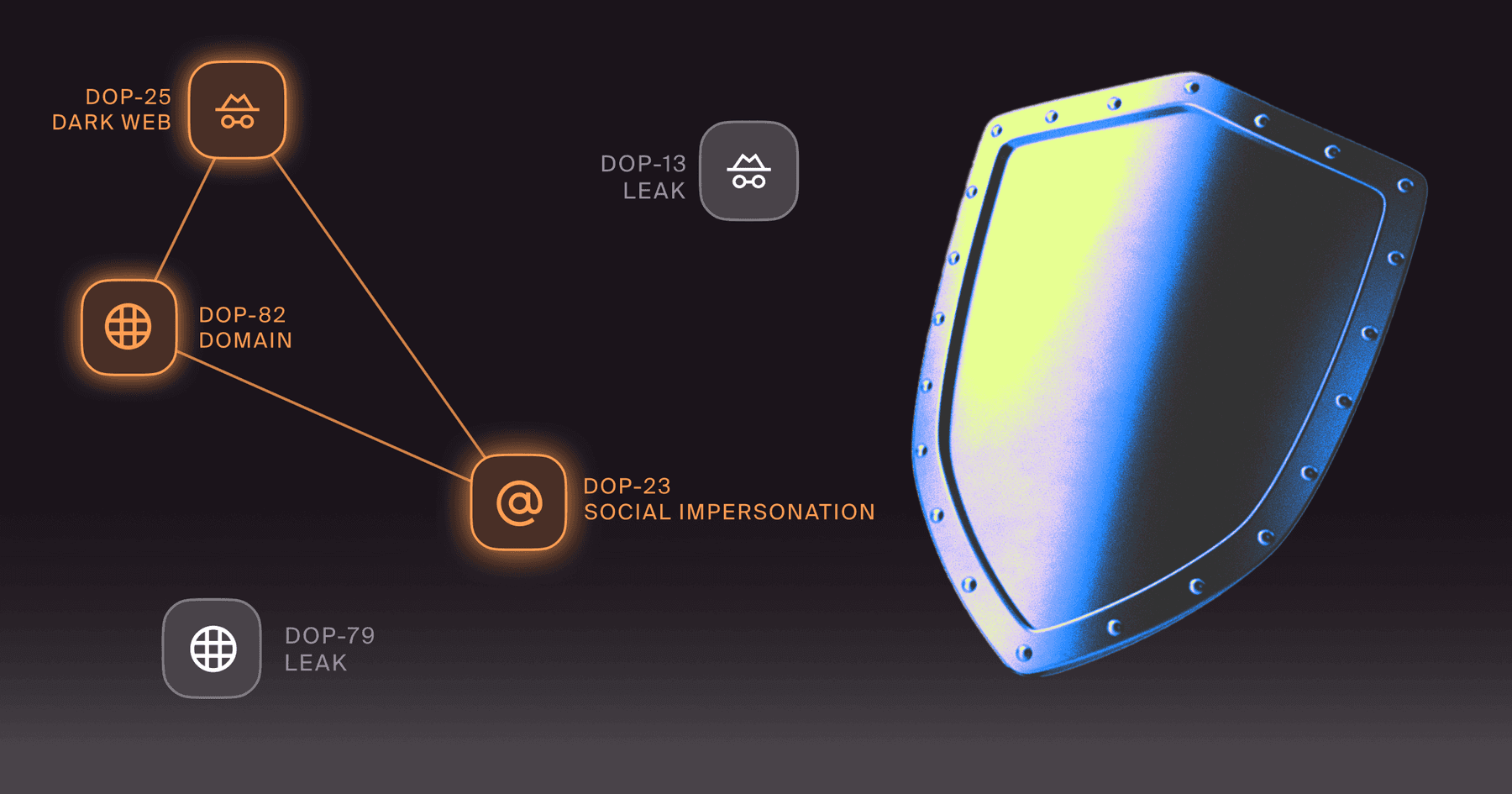
Doppel’s AI-native social engineering defense (SED) platform enables organizations to run highly sophisticated, multi-channel simulations specifically targeted at leadership teams.
We do not just send fake emails. We test your executives with the exact tactics, techniques, and procedures (TTPs) used by advanced threat actors.
This includes prolonged SMS relationships, highly targeted executive impersonation, and even realistic AI voice-cloned vishing calls.
By exposing your leadership team to interactive, dialogue-based scenarios, Doppel builds critical muscle memory at the highest levels of your organization.
When an executive experiences the psychological pressure of a simulated deepfake attack, they are infinitely more prepared to execute the 15-minute response plan when a real adversary strikes.
Is your executive team prepared to face an AI voice or video clone of your CEO? Get in touch with Doppel to see how our targeted leadership simulations can secure your financial perimeter.