In April 2026, a cybercrime platform named ATHR was discovered operating in the wild. It’s explicitly built to automate voice phishing (vishing) and telephone-oriented attack delivery (TOAD) campaigns at an unprecedented scale.
ATHR costs just $4,000 — with a 10% commission on any stolen funds — so a lone threat actor can purchase access to a fully autonomous, AI-driven call center.
This proves that social engineering is far more than a psychological parlor trick. It’s a highly optimized, heavily funded industry with its own subscription models and profit-sharing agreements.
Every security leader needs to recognize that the barrier to entry has plummeted, all while the sophistication of attacks skyrockets.
This is the era of phishing-as-a-service (PhaaS). Cybercriminals control the inputs, and AI does all the heavy lifting to deliver seamless social engineering attacks.
Social Engineering Doesn’t Need Sweat Equity Anymore
Look at how social engineering operated just a few years ago. In the past, executing a vishing attack required immense resources and significant human effort. Cybercriminals had to build their own infrastructure from scratch.
They had to register untraceable phone numbers, write convincing scripts, and manage the logistics of routing calls securely. They had to staff the operation, too.
Running a fraudulent call center meant relying on sweat equity. Cybercriminals hired, trained, and managed human operators, who needed a degree of fluency in the target’s language. They needed to think on their feet, and they needed the stamina to handle hundreds of calls a day without breaking character.
Between the massive overhead and sheer logistical friction, targeted voice phishing was reserved for high-value targets. It was effective, but the human element made this extremely difficult and expensive to scale.
AI has changed everything. The friction of hiring, training, and managing human operators is gone. Language barriers no longer exist. The cost of generating hyper-personalized, culturally accurate lures has dropped to near zero.
This leap in technology gave rise to PhaaS.
Skilled developers build malicious infrastructure, integrate AI components, refine conversational models, and then rent the entire platform to less technical threat actors for a flat fee.
Attackers with minimal technical skills pay for a software license, upload a list of targets, and click a button. The software takes care of the rest.
How ATHR Automates the Kill Chain
ATHR operates exactly like B2B software. It comes complete with a subscription tier, onboarding materials, and a sleek, centralized dashboard.
Here’s a look at how the platform functions under the hood:
- Telephone-Oriented Attack Delivery (TOAD): ATHR uses a built-in mailer to send out deceptive emails designed to bypass standard security filters. They contain a simple, plain-text phone number that prompts the victim to call to resolve a fake ‘security alert.’
- Branding Spoofing & Authenticity: ATHR enables attackers to spoof alerts from major brands such as Google, Microsoft, and Coinbase. Emails are generated to look structurally indistinguishable from real account notifications.
- Autonomous AI Agents: Threat actors utilizing ATHR don’t have to speak a single word. The platform provides pre-trained AI voice agents guided by detailed, system-level prompts.
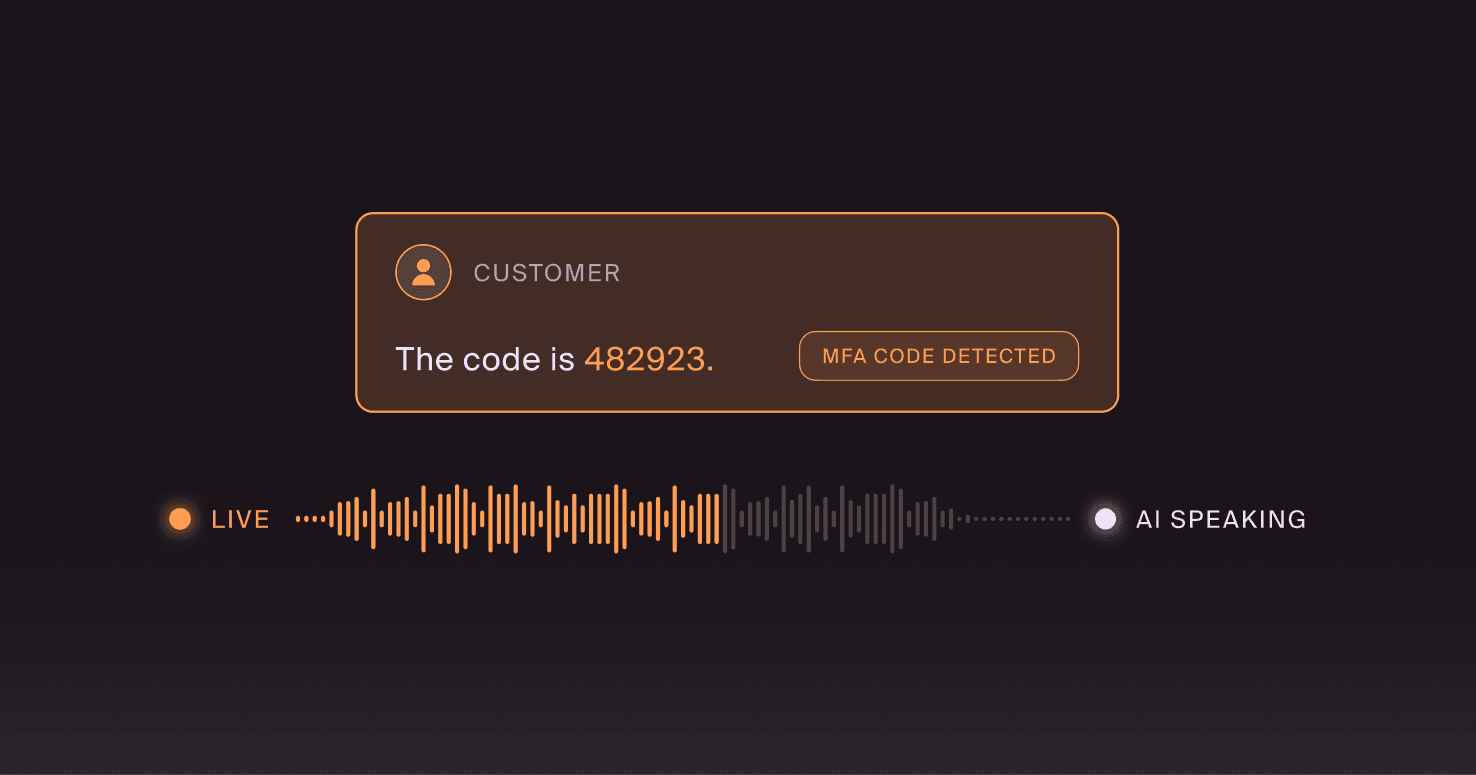
- Real-Time Synchronization: From a single screen, an attacker can distribute the initial TOAD emails and monitor live call transcripts in real time. They can instantly extract the six-digit multi-factor authentication (MFA) codes that the AI agents harvest from victims and redirect users to different phishing flows mid-conversation if necessary.
Consider the operational differences between legacy vishing attacks and those carried out with today’s cybercrime tools, like ATHR:
Attack Feature | Legacy Vishing | AI Vishing with ATHR |
Cost of Execution | High; requires paying human operations, and managing physical call centers | Low; flat software fee plus commission, without salaries or physical overhead |
Scalability | Limited strictly by the number of human operators on shift | Infinite; AI agents can handle thousands of concurrent, simultaneous calls |
Language Barriers | High; operators often struggle with localized dialects or cultural nuances | Zero; AI perfectly mimics regional accents, tone, and professional cadence |
Vector Integration | Siloed; email phishing and voice phishing were usually handled by different teams | Unified; platforms like ATHR integrate the email lure and the automated voice capture into a seamless kill chain |
Don’t Fall for the Defender’s Delusion
There’s a dangerous, widening gap between the reality of platforms like ATHR and organizations' readiness. Let’s call it the ‘defender’s delusion.’
Security leaders believe that because they host an annual security awareness training (SAT) seminar and send out simulated phishing emails every quarter, the workforce is prepared.
Legacy SAT conditions employees to act as human malware scanners. They’re taught to hover over URLs, check sender addresses for typos, and avoid clicking strange attachments.
But what happens when an employee faces a TOAD attack powered by ATHR?
There’s no link to hover over. The secure email gateway (SEG) scans the message, finds no malicious payloads, and delivers it straight to the inbox.
There are no grammatical errors, because the email was written by an LLM.
And the voice on the other end of the phone is professional, empathetic, flawless, and completely synthetic.
When an attacker uses a commercial AI platform, like ATHR, to run a real-time, multi-channel social engineering campaign, an employee armed with a compliance checklist is completely defenseless.
Closing the Gap: How to Defend Against AI-Powered Social Engineering
You can’t rely on static rules to fight dynamic AI. You need to build a culture of resilience that accounts for the fact that the payload isn’t just a link. It’s a conversation.
Here are the steps to harden the perimeter for human risk management (HRM):
- Shift Focus to Unmanaged Channels: Explicitly update your security policies to account for the risks of off-network communication. Employees must understand that threat actors use corporate email merely as a stepping stone.
- Implement Strict Out-of-Band Verification: Establish a rule that any request involving credentials, codes, or fund transfers must be verified through a secondary channel.
- Upgrade Simulation Capabilities: Run safe, controlled TOAD and vishing simulations against your workforce to expose employees to the psychological tactics and pacing used by AI voice agents.
- Provide In-the-Moment Coaching: Deliver micro-coaching to employees that explains how a simulated attack bypassed the email filter, how the phone call was designed to manipulate their sense of urgency, and what specific behavioral reflexes they need to practice.
Fight Software with Software: Social Engineering Defense (SED)
Attackers industrialized their deception. Now, it’s your turn to industrialize your resilience.
Just as attackers use phishing-as-a-service to scale exploits, CISOs and security teams need Doppel’s AI-native social engineering defense (SED) to scale their protection.
Doppel runs continuous, threat-informed simulations that mirror the exact strategies of platforms like ATHR. By testing your workforce against these sophisticated, multi-channel campaigns — including realistic AI voice clones and TOAD methodologies — Doppel validates your readiness. The AI-native SED platform even actively hunts and dismantles attacker infrastructure to neutralize threats before a malicious call ever reaches your workforce.
The adversaries upgraded their call centers, so it’s time to upgrade your social engineering defense.
Get a demo with Doppel to start validating your human perimeter against AI-powered social engineering platforms like ATHR.