Human risk management (HRM) or technical controls. What’s more important?
An organization spends $1 million implementing the gold standard of technical controls. The perimeter is seemingly locked down with phishing-resistant multi-factor authentication (MFA), enterprise-wide single sign-on (SSO), and a top-tier secure email gateway (SEG).
But there’s an attacker who spent just $5 on dark web-sold software for AI voice cloning. The cybercriminal scrapes a few seconds of audio from a recent podcast featuring the organization’s CFO.
Next, the attacker calls the organization’s IT help desk using the CFO’s cloned voice in real time, claims they’ve lost their phone while traveling, and demands an immediate MFA reset to access an urgent board presentation.
The help desk analyst, eager to assist the alleged executive in distress, bypasses standard protocol and resets the credentials.
In minutes, the million-dollar technical defense was completely bypassed by a five-dollar human conversation.
As adversaries bypass technical controls by targeting employees through social engineering attacks, HRM has become the defining factor in cyber resilience. It’s an integral part of social engineering defense (SED).
Mike Johnson, CISO at Rivian, recently posed a question that sparked an industry debate: If you had $1 to spend on your cybersecurity program, why would you spend it on phishing tests rather than on technical controls?
Budget is finite, and the pressure to justify every cent of security spend is immense. However, this ‘either-or’ choice is a trap.
Spending 100% of your budget on technical controls assumes those controls have a 0% failure rate.
In the era of AI-powered social engineering, that assumption is impossible. A winning security program doesn’t choose between technology and people. You need a continuous loop where human risk management reduces the blast radius when technical controls inevitably fail.
Rethinking the $1 Cybersecurity Dilemma
Answering the CISO’s question requires a shift away from a binary decision model and toward the anatomy of an attack lifecycle.
Technical controls and human behaviors aren’t competing for the same job. They’re stationed at different ‘checkpoints’ along the attack path. When we map out a resilient defense strategy, it’s clear why both are non-negotiable.
Here’s how industry-leading security teams categorize their investments.
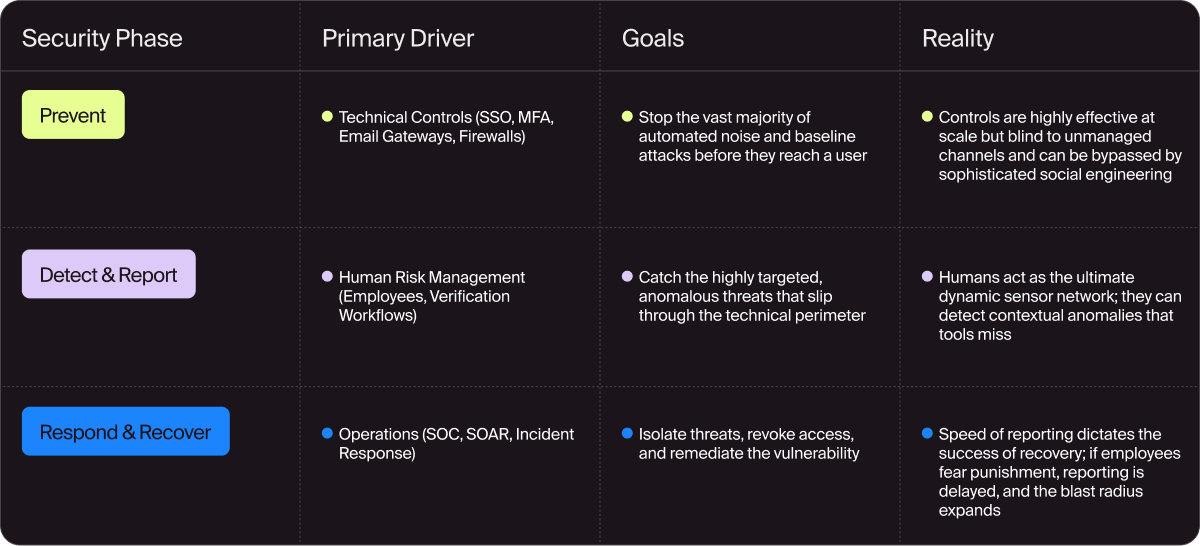
Technical controls are your first line of defense. But when a targeted, AI-crafted spear phishing campaign or a deepfake vishing attack bypasses the gateway, the technical control has already failed.
In that moment, the only thing standing between the attacker and your company’s data is an employee.
Where Each Approach Breaks Down in Isolation
Let’s dig deeper into the specific failure modes of each strategy when deployed in isolation, revealing why a blended approach between human risk management and technical controls is most effective.
Technical Controls: The Unmanaged Channel
Technical controls are exceptional at securing what they can see. An email gateway can quarantine a malicious attachment perfectly. SSO can enforce conditional access policies based on device posture.
But what happens when the attack doesn’t happen on corporate email?
Adversaries use a multi-channel strategy today. If they know your corporate email is locked down, they’ll pivot to unmanaged channels where your organization’s technical controls have zero visibility.
They’ll send a malicious text message to an employee’s personal phone, disguised as an urgent IT alert. They’ll reach out via WhatsApp claiming to be a recruiter. They’ll spoof a Zoom invite or use LinkedIn to deliver a payload.
Technical controls can’t prevent an employee from clicking a link on their smartphone while sitting on the couch at home, thereby compromising their corporate credentials. Only human intuition and training can defend against threats delivered outside the technical perimeter.
Security Awareness Training: The Compliance Illusion
The standard response to the human element was security awareness training, which often relied on a 45-minute video delivered annually to meet compliance requirements.
Training alone doesn’t prove readiness, though. Watching a video about how to identify a phishing email is like watching a video about how to fly an airplane. While it provides theoretical knowledge, it doesn’t prepare you for the cognitive load of a real-time crisis.
Annual training also suffers from rapid knowledge decay. When an employee faces a highly stressful, urgent request from a ‘manager’ six months after watching a training module, they’ll default to their desire to be helpful rather than their compliance training.
Phishing Simulations: The Vanity Metric
To counter the ineffectiveness of static training, the industry swung hard into phishing simulations. But simulating without context creates a toxic environment.
If you send your employees generic phishing templates, you’re teaching them to look for typos, not actual threats. Even worse, if you run hyper-realistic simulations but fail to provide immediate, constructive coaching when an employee clicks, you turn security into a ‘gotcha’ exercise.
Phishing simulations without coaching become vanity metrics for the security team to present to the board. They breed resentment, destroy psychological safety, and ensure that employees will actively hide their mistakes rather than report them to the SOC.
Human Risk Management in 2026: 5 Things a Program Needs for Success
What’s the answer if technical controls are incomplete and legacy training and simulations are incomplete?
Build a strategy for human risk management that continuously measures, tests, and supports human decision-making.
A successful HRM program is defined by these areas:
- Threat-Informed: Stop testing employees with templates from 2022. Phishing simulations should mirror the actual threat intelligence your security team is seeing today. If attackers are currently targeting your industry with fake ‘benefit enrollment’ portals or HR grievance lures, those are the exact scenarios your simulations should replicate.
- Role-Based: The marketing, engineering, and finance teams face completely different attack vectors. A one-size-fits-all approach is inefficient. Finance needs rigorous testing on invoice fraud and wire transfer protocols. Engineering needs simulations regarding fake GitHub repositories, rogue API keys, and unauthorized SaaS integrations.
- Multi-Channel: Because attackers have moved beyond emails, your phishing simulations must follow suit.
- Continuous: Annual or quarterly cadences are too slow. HRM should be an always-on, continuous loop. Micro-learnings, shortened and highly relevant lessons, delivered monthly, are significantly more effective at building muscle memory than a single, hour-long session.
- AI-Led:Generative AI is the attacker’s greatest weapon, and it’s also the defender’s greatest shield. AI-led HRM platforms dynamically adjust simulation difficulty based on an individual employee’s past performance.
Doppel, one of the leaders in HRM, has a platform built to mirror how attacks actually happen.
In 2026, Doppel introduced multistep simulations, QR codes in message-based simulations, and custom content creation. This means security teams move one step closer to closing the gap with attackers' real-world tactics.
Cybersecurity Budget: How to Allocate Your Spend
Returning to the CISO’s question: To allocate your finite cybersecurity budget while maximizing resilience, sequencing is everything. You need to build the foundation before you paint the walls.
Here’s a practical, phased approach to allocating the cybersecurity budget.
Phase 1: Establish the Baseline
Invest your initial budget in robust technical controls. Implement phishing-resistant MFA (like FIDO2 hardware keys), deploy SSO universally, and configure strict DMARC, SPF, and DKIM records for email.
If your employees are receiving thousands of low-effort spam emails a day, no amount of training will prevent an eventual breach. You need to filter the automated attacks first.
Phase 2: Deploy the Human Sensor Network
Once the technical baseline is established, allocate the next portion of your budget to a human risk management program. Acknowledge that your technical controls will be bypassed by highly motivated, well-resourced adversaries.
Invest in multi-channel phishing simulations and continuous, role-based coaching. The goal here is to transform your workforce from a liability into a distributed, dynamic sensor network that spots sophisticated attacks your gateways missed.
Phase 3: Build the Feedback Loop
Tie Phase 1 and Phase 2 together. Invest in SOAR that pipes human reporting directly into your technical defenses.
When an employee correctly identifies and reports a novel phishing lure via a Slack integration or an email plugin, that intelligence should automatically update your email gateway rules, block the malicious domain across the enterprise, and search for similar IOCs in other inboxes.
This is where the magic happens: Human intuition instantly updates technical controls, closing the loop.
Human Risk Management Checklist: Here’s What to Do Next
If you’re a security leader looking to upgrade your program, the sheer volume of options can be paralyzing. Focus on incremental, high-impact changes instead of trying to overhaul everything at once.
Multi-channel phishing simulations should be your top priority.
Take a hard look at your current simulation program. Is it 100% email-based? If so, you have a massive blind spot. Partner with a platform that allows you to safely test your employees’ reactions to SMS lures and instant messaging manipulations.
You’ll drastically reduce the likelihood that an employee’s first smishing attack will succeed by exposing them to multiple attack vectors in a safe, controlled environment.
- Audit Current Simulation Templates: Are they based on recent threat intel?
- Segment User Base: Are high-risk roles (such as executives, finance, and IT) receiving tailored scenarios?
- Review Reporting Friction: Does it take more than one click for an employee to report a suspicious message?
Closing the Loop on Cybersecurity Defense
As long as adversaries exist, the debate over human risk management and technical controls will continue. But the most forward-thinking security leaders have already realized that arguing over which is ‘better’ is missing the point entirely.
Security is about outcomes. It’s about readiness validation, risk prioritization, and defense alignment. It’s about acknowledging that while machines are excellent at following rules, humans are exceptional at recognizing context.
When you stop treating your employees as the weakest link and start equipping them to be the final (and strongest) layer of your defense-in-depth strategy, the entire paradigm shifts.
Technical controls will always fail, eventually. When they do, a well-managed, highly trained human workforce is the only thing that ensures a momentary lapse doesn’t become a headline-making catastrophe.
Ready to align your human defense with your technical controls? Doppel’s human risk management platform automates multi-channel simulation, contextual coaching, and readiness validation. Request a demo to see the HRM platform in action.